NCSC Recommendations and Best Practices for Cyber Essentials Certification
Table of Contents
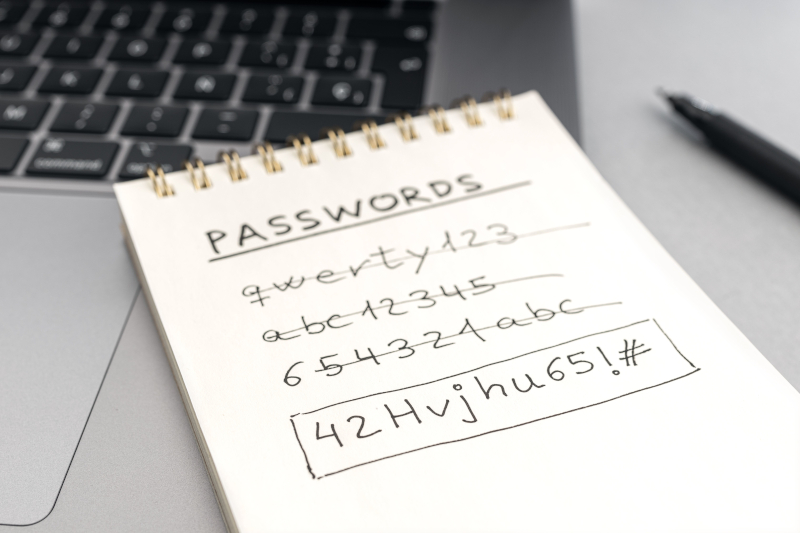
Password Security Pain
Passwords are a necessary headache in the modern world, and we often see conflicting advice on password strategies. In this article, we will explore how to create and manage secure passwords, taking into consideration the current recommendations by the NCSC (National Cyber Security Centre), which are used in the Cyber Essentials Certification programme.
Generic Password Security Advice
The most common advice is to never use the same password twice, ensure passwords are longer than a certain number of characters, and use a mix of character types (upper and lower case letters, numbers, and special characters). The NCSC recommends a minimum password length of 12 characters, or 8 characters if multi-factor authentication (MFA) or automatic blocking of common passwords is enabled. But how do you come up with and remember so many passwords? To a large extent, this can be addressed with the use of password managers and saving passwords in relevant applications, such as web browsers. As long as you keep your password manager and software up to date, you should be relatively secure.
Three Random Words Password Strategy
However, there will be passwords that you need to remember. In such cases, the NCSC recommends using the Three Random Words strategy. This approach encourages creating passwords that are fairly long and of unpredictable length. It can also help meet other password complexity requirements by using a special character like a semi-colon to separate the words, capitalising a character in each word, and replacing particular letters with numbers.
Changing Passwords
For a very long time, the advice has been to change passwords regularly. However, this is now being actively challenged, and the NCSC advises disabling this requirement if possible. The theory is that being forced to change your password regularly leads to less secure passwords, with users often just changing a number at the end and writing them down. The only time you really need to change your password is when you believe it has been compromised.
Multi-Factor Authentication (MFA)
Sometimes referred to as Two-Factor Authentication, MFA should be used wherever it is available, particularly for cloud services such as Microsoft 365. A random number generator, such as Google’s Authenticator mobile app, or biometrics (e.g. fingerprint or facial recognition), is preferred. Email and SMS text messages are considered less secure, but any form of MFA is better than none.
Password Managers
Using a password manager can significantly simplify the process of maintaining strong, unique passwords for every account. These tools can generate, store, and auto-fill passwords, reducing the burden on the user to remember them.
Avoiding Phishing Attacks
Even the strongest password can be compromised if you fall victim to a phishing attack. Be cautious of emails or messages that ask for personal information or direct you to log in to a website. Always verify the source and look for signs of phishing, such as unusual sender addresses or suspicious links.
Secure Backups
Ensure that you have secure backups of important data. In the event of a cyber attack, such as ransomware, having a recent backup can be crucial to recovering your information without paying a ransom.
Regular Software Updates
Keeping your software and operating systems up to date is crucial for security. Updates often include patches for vulnerabilities that could be exploited by attackers.
For Mobile Devices
For mobile devices, the NCSC recommends a PIN length of at least six characters to unlock the device. Additionally, ensure that your device’s operating system and apps are regularly updated to protect against vulnerabilities.
The Password Security Plan
In this article we have looked at how to create and manage secure passwords and provided additional advice on keeping your passwords protected, in accordance with UK Government advice from NCSC. This provides a critical component of your cyber security and staying safe online.